Engineering the Pure Signal: 4 Open-Source Tools to Bulletproof Your Workflow
01In both music production and software architecture, the goal is exactly the same. You treat code like a recording session: strip the noise until only the purest signal remains in the brand identity.
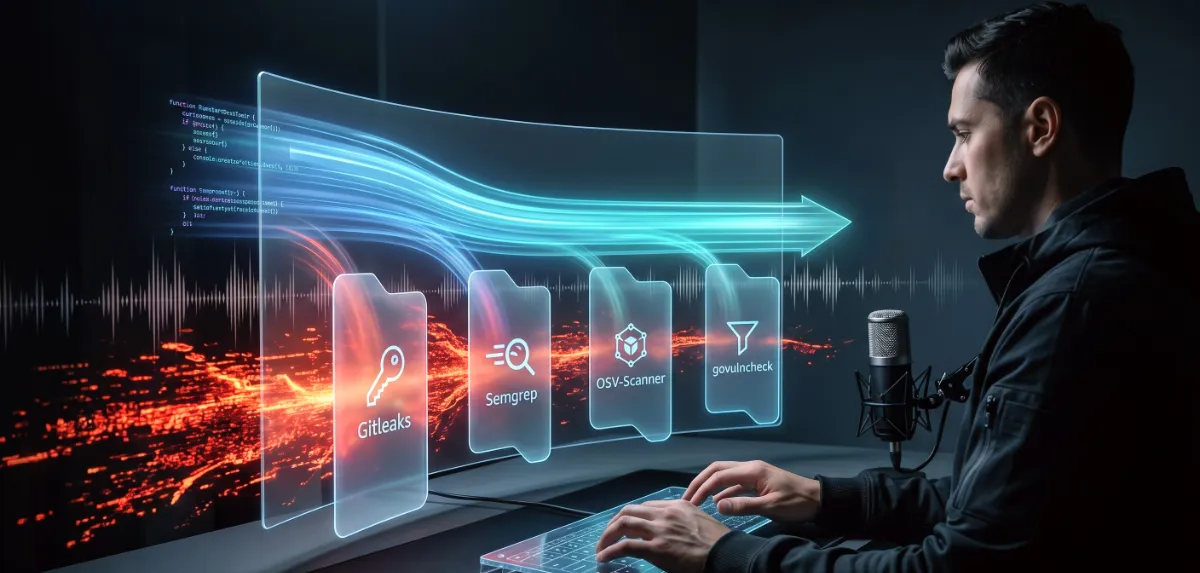
But in modern development, "noise" isn’t just a humming guitar cable or unoptimized Next.js rendering. Noise is a leaked API key. It’s a vulnerable third-party package buried deep in your node_modules. As we integrate more AI tools and local-first development environments into our daily grind, the sheer volume of code we produce is multiplying. We need a way to filter out the risks before they ever reach production. A recent breakdown on Dev.to highlighted some fantastic open-source security utilities, which sparked my thinking on how we integrate these concepts into a high-performance workflow at Lizard Interactive Online. Here are four essential tools to act as the ultimate noise gates for your codebase.
02Gitleaks: The Unforgiving Noise Gate
Hardcoding secrets is the equivalent of leaving the mic hot in a noisy room. Once a JWT or database credential hits your Git history, the take is ruined, and you have to roll the keys. Gitleaks is the industry standard for catching this. Instead of just scanning your current working directory, it parses your entire Git history to detect exposed credentials. Dropping this into your local Linux development environment as a pre-commit hook ensures that no sensitive keys ever leave your machine. It’s a relentless safety net that keeps your commits clean.
03 Semgrep: The Intelligent Mix Engineer
Traditional grep searches are blunt instruments—they look for exact text matches, which generates a massive amount of false positives. Semgrep is different. It understands the actual syntax and semantics of your code. Whether you are building complex React components or piping data from an MCP server, Semgrep can detect vulnerable logic patterns, not just text strings. If you set a rule to flag unsanitized inputs hitting an execution command, Semgrep catches it, regardless of what variables are named. It catches architectural missteps before they hit the CI/CD pipeline
04OSV-Scanner: The Dependency Auditor
If you are pushing for 100/100 Lighthouse scores, you already know that every dependency you add bloats your bundle. But dependencies also expand your attack surface. Built by Google, OSV-Scanner taps into the Open Source Vulnerability (OSV) database. You point it at your lockfile, and it instantly outlines which libraries are harboring known CVEs. Crucially, it ranks these vulnerabilities by severity and depth, giving you a prioritized, actionable list to patch your application rather than a chaotic wall of red errors
05If you are pushing for 100/100 Lighthouse scores, you already know that every dependency you add bloats your bundle. But dependencies also expand your attack surface. Built by Google, OSV-Scanner taps into the Open Source Vulnerability (OSV) database. You point it at your lockfile, and it instantly outlines which libraries are harboring known CVEs. Crucially, it ranks these vulnerabilities by severity and depth, giving you a prioritized, actionable list to patch your application rather than a chaotic wall of red errors
Vulnerability scanners are notoriously noisy, often throwing alerts for vulnerabilities inside libraries that your code never even touches. If you work in Go, govulncheck solves this elegantly. It analyzes your call stack and only flags an alert if your specific code paths actually call the vulnerable function. This drastically improves the signal-to-noise ratio, ensuring you spend your time fixing real threats instead of chasing ghosts in unused code.
06The AI Era Requires Better Filters
AI is incredible at writing the patch, but the LLM doesn't take the blame for a production outage—you do. Static scanners handle the known vulnerabilities, but to catch the subtle logic regressions introduced by AI, we have to enforce strict, commit-level reviews. Tools like git-lrc are bridging this gap, providing 60-second micro-reviews on staged diffs before they are committed. By combining foundational scanners with AI-assisted verification, you ensure that your deployment pipeline remains pristine. Keep the noise out, and ship only the pure signal.